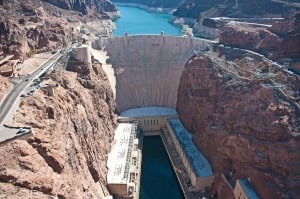
The U.S. Bureau of Reclamation has chosen OSIsoft’s PI system for operational improvements at the Hoover, Davis, and Parker dams.
All three of the dams are situated on the Colorado River and supply power and water to around two million customers in the Southwest.
See also: How Cognitive Computing Improves the Call Center Customer Experience
“By serving up real-time information on operating performance, power demand, asset conditions and cybersecurity, the PI System will help Bureau engineers better match power production with demand, minimize water losses and improve visibility of operations,” said Steve Sarnecki, Vice President of Federal for OSIsoft. “All while doing so in a secure and proven software infrastructure already in use throughout the Federal Government.”
The PI system will provide real-time insights to workers at the three dams on equipment health, highlighting maintenance issues before they become a major issue. OSIsoft said the platform will also improve security and reliability of equipment across the complex.
“Being able to access, understand and use accurate, real-time data is absolutely essential in the water and power industries. With the PI System, the Bureau can take into account factors like demand variation, reservoir levels and changing weather patterns for daily operational decisions,” added Gary Wong, Industry Principal for Water at OSIsoft.
“Real-time data from the PI System will also provide a means to craft long-term strategies for such balancing water distribution for a substantial portion of the Southwest.”
The PI system has also been adopted by the Western Area Power Administration (WAPA) for its common data infrastructure. WAPAs Desert Southwest region transmits power from the three dams to 45 electric cooperatives and 23 Native American tribes.